Product Description
Abstract
The nature and scope of identity theft have changed with advancements in computer technology and evolution of the Internet. Hackers have become a new breed of criminals, whose targets are unsecure computer systems, payment databases, and card numbers. With the right malware programs and an instant message service, a group of like-minded hackers can now commit large-scale data breaches that lead to millions of dollars in losses for companies, financial institutions, and individual customers. Often, the culprits are caught when it is much too late—after significant, often irreparable, damage has been done to the victims.
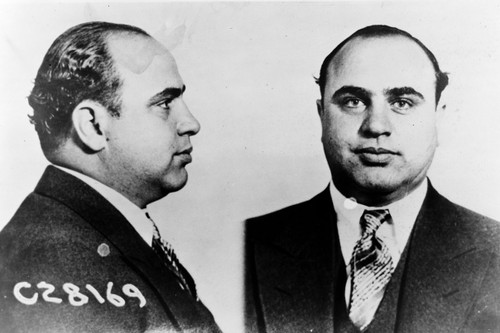
This case study will attempt to make these generalizations more concrete and understandable through a comprehensive analysis of the greatest cybercrime committed to date: Albert Gonzalez’s Operation Get Rich or Die Tryin’, conducted while Gonzalez was an informant for the Secret Service. Gonzalez’s informant role began in 2003, when detectives caught him withdrawing cash at an ATM using cards with stolen numbers. To avoid prosecution, he agreed to cooperate: he helped the Secret Service take down Shadowcrew, a ring of cybercriminals of which Gonzalez had been a major part. After that successful sting operation, Gonzalez went on the Secret Service payroll, earning $75,000 a year to aid other ongoing investigations.
As an informant, Gonzalez learned the weak points of the government’s cybercrime defenses and saw an opportunity. Gonzalez reconnected with hackers under the name Green Hat Enterprises, and began intercepting the wireless transmissions of financial information from retail stores. Over time, Green Hat Enterprises moved toward more efficient means of data acquisition, stealing millions of credit card numbers. Gonzalez knew from his prior arrest that it would be dangerous to cash out the stolen card numbers himself, so he sold information to other criminals to avoid getting caught. Maksim Yastremskiy, Gonzalez’s contact in the Ukraine, created counterfeit cards using supplies from China. But when Yastremskiy was arrested, the Secret Service got leads on Yastremskiy’s associates, and found out that Gonzalez had double-crossed them.
The case documents Gonzalez’s actions, the logistics of data acquisition (track 2 credit card data, wireless networks, corporate databases, Structured Query Language, Point-of-Sale Terminals) and money laundering, Gonzalez’s downfall, and the plea bargain. The case ends with recommendations for cybercrime prevention.
Learning Objectives
- Understand the mechanisms of cybercrime.
- Analyze the facts of a cybercrime to identify opportunities to prevent large-scale data breaches.
- Evaluate how the relationship between law enforcement and informants can be structured to prevent cybercrime.
Subjects Covered
credit card fraud, identity theft, informants, cybercrime, hackers, data acquisition, money laundering, plea bargains, track 2 data
Setting
Geographic: Miami, United States; Ukraine
Industry: Organized cybercrime; financial information
Event Start Date: 2003
Accessibility
To obtain accessible versions of our products for use by those with disabilities, please contact the HLS Case Studies Program at hlscasestudies@law.harvard.edu or +1-617-496-1316.
Educator Materials
Watermarked educator copies for this product are available free of charge to educators and staff at non-profit institutions. Please create an account or sign in to gain access to these materials.
Note: It can take up to three business days after you create an account to verify educator access. Verification will be confirmed via email.
Copyright Information
Please note that each purchase of this product entitles the purchaser to one download and use. If you need multiple copies, please purchase the number of copies you need. For more information, see Copying Your Case Study.